Software development constantly evolves. Consequently, engineering leaders face new organizational challenges. Specifically, they must manage growing infrastructure complexity. Therefore, teams urgently need better delivery structures. Platform engineering trends 2026 address these exact hurdles directly. Furthermore, this approach fundamentally changes software creation. Organizations no longer rely on fragmented toolchains. Instead, they build cohesive product ecosystems. Indeed, we see a massive shift globally. Why Internal Developer Platforms Matter Now Developers often struggle with infrastructure management. In fact, managing manual deployments drains valuable coding time. Fortunately, internal developer platforms solve this problem beautifully. These modern portals provide self-service tools for engineers. Therefore, developers can provision resources independently. Additionally, they bypass traditional operations bottlenecks. This newfound autonomy heavily boosts overall team productivity. You can explore our consulting on this at IT Touch. The New DevOps Operating Model Historically, DevOps promised seamless cross-functional team collaboration. However, scaling these practices proved incredibly difficult. Thus, a new DevOps operating model emerged recently. Platform engineering trends 2026 highlight this crucial transition clearly. Forward-thinking teams treat their platform as a real product. Consequently, software developers become the primary internal customers. Platform engineers actively gather qualitative user feedback. Subsequently, they refine the shared tools continually. Learn more about adopting this structure at IT Touch. Prioritizing Developer Experience Optimization Burnout remains a serious tech industry issue. Therefore, developer experience optimization is absolutely crucial today. Good platforms proactively reduce crippling cognitive load. Furthermore, they provide standardized and secure “golden paths”. These paved roads guide software developers safely. Indeed, they ensure strict security without causing friction. We track these vital metrics using CNCF guidelines. Ultimately, happier developers write significantly better code. Discover our unique experience optimization strategies via IT Touch. Implementing Platform Engineering Trends 2026 Transitioning requires careful and deliberate organizational planning. Initially, you must secure executive leadership support. Next, identify your biggest daily delivery bottlenecks. Only then should you design the core platform architecture. Moreover, you must treat internal platforms like external products. We highly recommend studying Team Topologies for structural guidance. Start small and iterate based on clear metrics. Read our successful implementation case studies at IT Touch. Future-Proofing Your Delivery Systems Adopting platform engineering trends 2026 guarantees business resilience. Ultimately, modern enterprises must ship user features faster. Moreover, they cannot sacrifice underlying system reliability. Standardized workflows beautifully balance these competing business needs. In summary, this strategic investment represents the future. Companies ignoring this shift will inevitably fall behind. Start building your dedicated platform team today. Partner with our experts at IT Touch to begin immediately.
Strategic Cloud Repatriation: The Shift to Private Infrastructure
Strategic cloud repatriation is rapidly becoming the defining technology trend of 2026 for forward-thinking enterprises. Organizations currently realize that the public cloud is not always the most cost-effective solution for every workload. Consequently, many tech leaders are moving specific applications back to on-premise data centers or private clouds. This massive shift prioritizes cost control, performance stability, and enhanced security. Why Business Leaders Choose Private Cloud Infrastructure Cost reduction drives this major architectural change. Public cloud fees often scale unpredictably, but private cloud infrastructure offers fixed, manageable costs for stable workloads. Furthermore, data gravity concerns are pushing companies to keep sensitive information closer to home. You can gain better oversight by hosting data internally. Optimizing Hybrid Cloud Costs Effectively Strategic cloud repatriation does not mean abandoning the public cloud entirely. Instead, it fosters a balanced hybrid approach. You maintain flexibility for bursting workloads while securing core data on dedicated hardware. This balance ensures you only pay for what you truly need. For more insights on balancing these environments, visit our cloud optimization services. Enhancing Control Through Data Sovereignty Solutions Regulatory compliance is stricter than ever before. Therefore, strategic cloud repatriation provides the ultimate answer to data residency laws. By storing data locally, you ensure it never crosses borders illegally. This control minimizes legal risks significantly. Learn more about our specific security protocols that align with these needs. Implementing Your Repatriation Plan Transitioning requires careful planning. First, identify which applications are costing the most in the public cloud. Next, assess your internal team’s capability to manage hardware. Finally, partner with experts who understand strategic cloud repatriation. Our team at IT Touch can guide this complex process. You should also consider the hardware lifecycle. Modern servers are more power-efficient, supporting green IT initiatives. Read about sustainable tech on Green IT News.
The Rise of Geospatial Digital Twins for Infrastructure Resilience
The global landscape for urban planning is changing rapidly this year. Modern developers now prioritize long-term durability over simple aesthetic design. Geospatial digital twins for infrastructure resilience have emerged as the primary tool for achieving these modern goals. Unlike traditional 2D maps, these living replicas integrate real-time sensor data with high-fidelity 3D models. Enhancing Urban Planning with 3D Reality Capture The shift toward 3D reality capture allows engineers to visualize potential failures before they happen. By using dynamic GIS asset management, cities can monitor bridge stability and power grid health simultaneously. This proactive approach reduces maintenance costs significantly. Many organizations now use these tools to simulate flood patterns and extreme weather impacts. Consequently, geospatial digital twins for infrastructure resilience help leaders make data-driven decisions during critical emergencies. Building Sustainable Cities via Simulation Sustainability is no longer a secondary concern for modern tech firms. Developers leverage urban infrastructure simulation models to optimize energy consumption across entire districts. These digital replicas allow for the testing of “what-if” scenarios without risking physical assets. This method ensures that new constructions meet strict environmental standards. Using geospatial digital twins for infrastructure resilience ensures that every new project contributes to a greener, safer urban environment. Future-Proofing with Integrated Spatial Data Integration is the final piece of the modern geospatial puzzle. When companies combine satellite imagery with ground-level LiDAR, the resulting intelligence is unparalleled. This fusion creates a comprehensive view of the built environment. As we move further into 2026, geospatial digital twins for infrastructure resilience will remain the backbone of global development. They provide the clarity needed to protect our shared future. Resource Links Outbound References: Internal Resources (ITTouch):
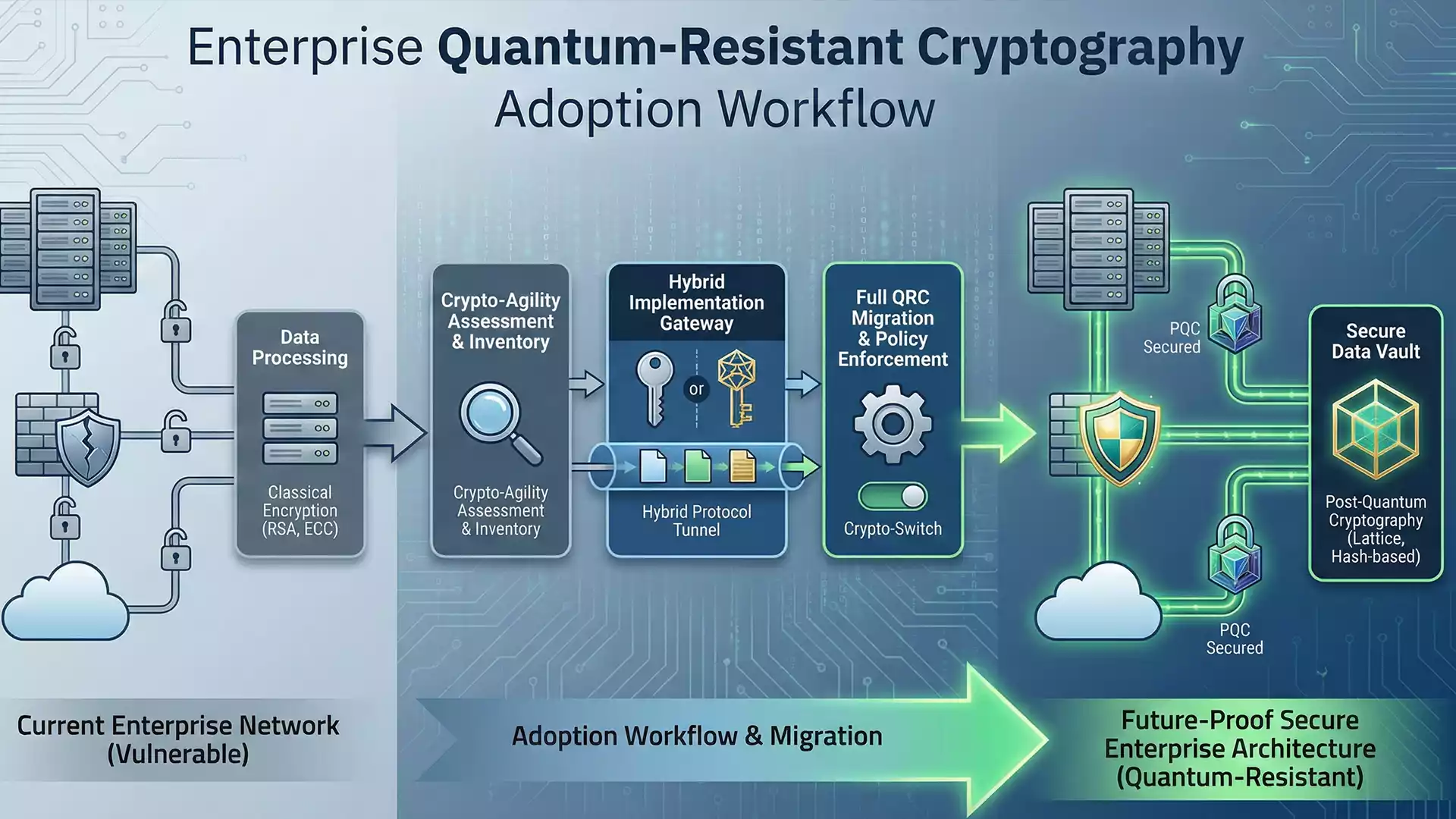
Quantum-Resistant Cryptography Adoption: A 2026 Imperative
A 2026 Imperative Quantum-Resistant Cryptography Adoption: Securing the Future The digital security landscape is shifting rapidly this year. Quantum-resistant cryptography adoption has emerged as a critical priority for forward-thinking enterprises. Traditional encryption methods are becoming vulnerable to powerful new computing systems. Therefore, businesses must act now to protect their sensitive information from future decryption attacks. Industry leaders effectively call this the “Harvest Now, Decrypt Later” threat. Attackers steal encrypted data today, waiting for quantum computers to break it later. Consequently, implementing quantum-resistant cryptography adoption strategies immediately is the only viable defense. Experts at IT TOUCH (https://ittouch.io/services/cybersecurity) help organizations navigate this complex transition. We assess your current risk levels. Furthermore, we design roadmaps that align with evolving global standards. Implementing Post-Quantum Security Standards Regulatory bodies are finally finalizing their guidelines. The NIST (National Institute of Standards and Technology) has released confirmed algorithms for general use. Adhering to these post-quantum security standards ensures your infrastructure remains compliant and secure. Transitioning is not a simple “flip of a switch.” It requires a hybrid approach initially. Systems must support both classic and new encryption methods simultaneously. This phase prevents service disruptions during the upgrade process. Our consulting team (https://ittouch.io/services/consulting) specializes in managing these delicate migrations. Moreover, major tech firms like IBM Quantum are already integrating these protocols. They understand that trust is the currency of the digital age. Thus, failing to upgrade could result in significant reputational damage. Achieving Cryptographic Agility Solutions Static security measures are no longer sufficient. You need cryptographic agility solutions to survive in 2026. This approach allows you to switch encryption methods quickly without rewriting applications. Therefore, if a specific algorithm is compromised, you can pivot instantly. This agility is a core component of modern infrastructure management (https://www.google.com/search?q=https://ittouch.io/solutions/infrastructure). It empowers your IT teams to react to threats in real-time. Additionally, agencies like CISA emphasize agility as a cornerstone of cyber resilience. We recommend reading our detailed blog posts (https://ittouch.io/blog) for technical deep dives. Staying informed is your first line of defense. Also, consider how future-proof data protection impacts your bottom line. Preparing Your Organization Today Do not wait for a quantum breach to make headlines. Start your quantum-resistant cryptography adoption journey today. Review your data inventory. Identify long-term secrets that need immediate protection. Check out The Quantum Insider for the latest industry news. They track the speed of hardware advancements closely. Similarly, MIT Technology Review offers excellent insights into the timeline of these technologies.
Satellite Direct-to-Device Connectivity: A New Era
The telecommunications landscape is shifting dramatically in early 2026. Satellite Direct-to-Device connectivity has emerged as a groundbreaking innovation, fundamentally changing how we stay connected. This technology bypasses traditional cell towers entirely. Instead, it links standard mobile phones directly to low-earth orbit satellites. Consequently, users can access services in dead zones where terrestrial signals fail. Industry leaders are rapidly deploying these systems to eliminate coverage gaps. For instance, SpaceX has accelerated its Starlink Direct to Cell rollout. This capability allows unmodified smartphones to text, call, and browse data globally. Therefore, remote regions, maritime environments, and rural communities finally gain reliable access. At IT TOUCH, we analyze how such innovations impact enterprise infrastructure. Our telecom consulting services help businesses prepare for this connectivity revolution. Integrating these capabilities ensures your workforce remains operational anywhere. Understanding Non-Terrestrial Network Technology The core of Satellite Direct-to-Device connectivity lies in advanced non-terrestrial network technology. Engineers design these satellites to act like “cell towers in space.” They utilize specific spectrum bands that existing phones can detect. Thus, you do not need expensive, bulky satellite phones anymore. This seamless integration is crucial for mass adoption. 3GPP, the global standards organization, recently standardized these protocols in Release 18. This standardization ensures interoperability across different network providers. As a result, seamless roaming between land-based and space-based networks is now possible. Bridging Gaps with Global Mobile Coverage Solutions Reliability defines this new wave of Satellite Direct-to-Device connectivity. Emergency services benefit immensely from this resilience. For example, hikers or disaster victims can send distress signals without local grid infrastructure. AST SpaceMobile is another key player pushing these boundaries. Their massive satellite arrays deliver broadband speeds directly to your pocket. Businesses must also adapt their logistics and tracking systems. Our connectivity solutions provide the framework to leverage these global mobile coverage solutions. Enhanced tracking visibility transforms supply chain management efficiency. The Mechanics of Space-Based Cellular Broadband Technically, Satellite Direct-to-Device connectivity involves complex signal processing. Satellites move rapidly relative to the ground, creating Doppler shifts. Advanced software compensates for these shifts instantly. Additionally, beamforming technology focuses signals directly on specific users. Regulatory bodies are currently adjusting frameworks to accommodate this. The Nigerian Communications Commission has opened consultations to manage spectrum allocation effectively. This proactive approach highlights the technology’s global significance. You can learn more about navigating these regulatory changes on our industry insights blog. Staying informed helps you avoid compliance pitfalls. Future Implications for Tech Infrastructure The proliferation of Satellite Direct-to-Device connectivity challenges current infrastructure models. Mobile network operators must partner with satellite firms rather than compete. GSMA reports that such partnerships will drive future revenue growth. We recommend reviewing your current hardware strategy. Visit our about us page to see how we stay ahead of these trends. Furthermore, if you need specific advice, please contact our team for a detailed assessment. Ultimately, space-based cellular broadband is not just a trend; it is the future of ubiquity.
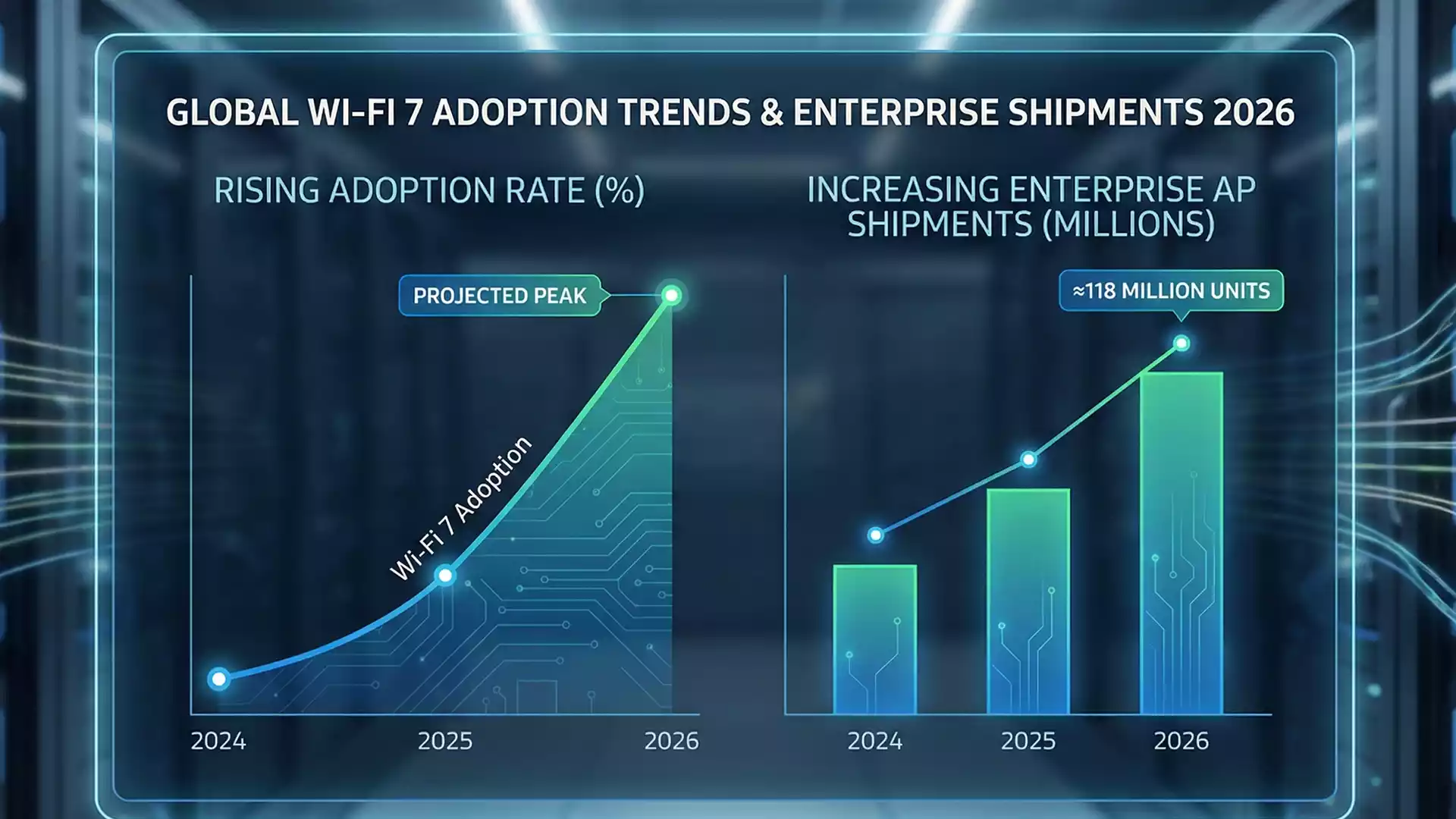
Wi-Fi 7 Adoption Trends 2026: The New Standard for Connectivity
The landscape of wireless technology is shifting dramatically this year. Wi-Fi 7 adoption trends 2026 indicate a massive surge in global uptake. Consequently, businesses are moving away from older standards to embrace this robust connectivity. Experts predict that shipments of Wi-Fi 7 access points will reach nearly 118 million units by the end of 2026. This growth highlights a critical pivot toward reliability over simple raw speed. Organizations are prioritizing stable connections for their critical operations. Therefore, IT leaders are investing heavily in upgrading their networks. IT TOUCH Limited (https://ittouch.io/) assists these forward-thinking companies in navigating complex infrastructure changes. Furthermore, the focus is now on reducing latency. Low latency is essential for real-time applications like industrial automation and immersive virtual collaboration. Next-Generation Wireless Connectivity for Enterprises New hardware is flooding the market. As a result, enterprises have more choices than ever before. Wi-Fi 7 adoption trends 2026 show that the 6GHz spectrum is becoming the new battleground for efficiency. This “clean” spectrum allows for wider channels. Thus, data flows faster and with less interference from neighboring networks. However, simply buying new routers is not enough. Companies need a comprehensive strategy. Comprehensive planning ensures that new devices integrate seamlessly with legacy systems. Network World reports that educational institutions and large public venues are leading this charge. They require high-density performance that older Wi-Fi 6E standards struggled to maintain under heavy loads. Moreover, the technology-driven solutions (https://ittouch.io/) provided by experts help mitigate installation risks. Proper configuration is vital. Without it, the benefits of the 320 MHz channel width remain unlocked. Additionally, businesses must consider security. The new standard mandates WPA3 security protocols, ensuring that faster connections do not compromise data safety. Enterprise Network Infrastructure and Future-Proofing Reliability is the core promise of the new standard. Wi-Fi 7 adoption trends 2026 suggest that “multi-link operation” (MLO) is a game-changer. MLO allows devices to send data across multiple bands simultaneously. This capability drastically reduces connection drops. For industries relying on uninterrupted data, this is revolutionary. For instance, healthcare and manufacturing sectors benefit immensely. Wireless Broadband Alliance notes that these sectors are accelerating their hardware refresh cycles. They cannot afford downtime. Consequently, they turn to reliable network partners (https://ittouch.io/) to manage these critical upgrades. Transitioning to this level of connectivity requires expertise. IDC Research data suggests that adoption rates are outpacing initial 2025 forecasts. This acceleration puts pressure on IT departments. They must act quickly to stay competitive. 6GHz Spectrum Deployment and Beyond The future looks even faster. While Wi-Fi 7 adoption trends 2026 dominate the headlines, early prototypes for Wi-Fi 8 are already appearing. Nevertheless, the current focus remains on maximizing the utility of Wi-Fi 7. To leverage these benefits, businesses need robust tech support services (https://ittouch.io/). Wi-Fi Alliance certifies these devices to ensure interoperability. Therefore, compatibility issues are minimizing. Finally, the push for better connectivity is global. ABI Research forecasts continued growth in mesh networking equipment. This ensures consistent coverage in sprawling office campuses. By partnering with experienced IT consultants (https://ittouch.io/), your business can seamlessly ride this wave of innovation. The time to upgrade is now.
Agentic AI Systems: The 2025 Tech Revolution
Agentic AI systems have officially moved beyond experimental labs. As of today, December 23, 2025, these intelligent protocols are reshaping the global workforce.
Publish a post via email
To publish a post via email, follow these steps: Please note that you can only post by email to one site at a time. If you try to post to multiple email addresses at once, only the first one will be used. Remove email signature Post by Email will remove: Include attachments Post by Email supports sending PDF files and images as attachments. PDF attachments sent using Post by Email will appear at the bottom of your post, accessible by a link. Image attachments will be included in your post as follows: Multiple galleries and single images are allowed in the same post. You can use the [nogallery] shortcode to disable all galleries in a post. Shortcodes Shortcodes can be embedded in your email to configure various aspects of the published post. Include shortcodes anywhere in the body of your email, making sure they are in lowercase, and with no spaces between the left square bracket and the shortcode content. The following shortcodes can be used when posting by email: Add categories [category x,y,z] Add existing categories to your post, or create new categories. Categories must be comma separated. [category holidays, main-dishes] Note: it’s possible to add categories by matching existing category slugs. For example, ‘main-dishes’ may add the ‘Main Dishes’ category if it exists. If the ‘main-dishes’ category did not exist, however, then a new category with the slug and name ‘main-dishes’ would be created instead. Add tags [tags x,y,z] As with categories, you can add any number of tags to your post, each separated by a comma. Add existing tags, or create new ones. [tags one potato, two potato, three potato, more] In this example, four tags will be added to your post: ‘one potato’, ‘two potato’, ‘three potato’, and ‘more’. Delay publication of your post [delay +1 hour] The delay shortcode will accept any time allowed by PHP’s strtotime function. For example, you can use the following to delay your post by one hour, or two days, respectively. [delay +1 hour][delay +2 days] Change your post status [status publish | pending | draft | private] Sometimes you may want your post to be private, or to be reviewed by yourself or someone else before being published. To do this, you can use the [status] shortcode to set the post status. [status private] This will post your content with a ‘private’ status.[slug some-url-name] Specify a post title [title Your post title] By default, the title of your post will be taken from the subject line of your email. In some instances, such as when sending an email from some cell phones or via a MMS-Email gateway, you may not be able to provide a subject. In these cases, you can set your post title from inside the email with a shortcode: [title My Fancy Post] This will set the title of your post to ‘My Fancy Post’. Withhold email signature or other content [end] Everything after the [end] shortcode is ignored. If you use this, make sure it’s on its own line with a blank line above it. Change auto‑gallery options – replaces the auto-gallery with a slideshow [nogallery] – disables the auto-gallery and displays all images inline Disable comments on a post [comments on | off] Use the above short code to turn comments on or off for a post. Publish a Post on Your Website via Email In today’s fast-paced digital environment, efficiency is key. Logging into your website’s backend every time you need to share an update, an idea, or a new article can be time-consuming. At iT TOUCH LTD, we offer a streamlined solution that transforms your content workflow. With our innovative service, you can publish a post on your website via email, allowing you to update your site from any device, anywhere in the world. Seamless Content Creation from Any Device Our system is built for ultimate convenience. The process is as simple as sending a standard email. We provide you with a unique, secure email address linked directly to your website. From any email client that supports rich text or HTML—be it on your laptop, tablet, or smartphone—you can compose your content. The email’s subject line automatically becomes your post’s title, and the body of the email becomes the post’s content. This intuitive method removes technical barriers, making it easier than ever to publish a post on your website via email, whether you’re in the office or on the move. Effortless Media and Content Integration A great post often includes more than just text. Our service intelligently handles your attachments to create rich, engaging content. Advanced Control with Simple Commands For those who need more granular control over their content, our Post by Email service supports a powerful set of shortcodes. These simple, text-based commands can be placed anywhere in your email body to manage every aspect of your post before it goes live. Ready to revolutionize your content workflow? Contact iT TOUCH LTD today to enable this powerful feature on your website.
IT Touch Limited: Empowering Businesses with Cutting-Edge Solutions for the Digital Age
We are dedicated to offering cutting-edge solutions for businesses. IT Touch Limited offers a wide range of services. Partner with us today.
ICT solutions: Empowering Businesses with Technology Solutions
Are ICT solutions important for businesses in this digital age? As technology continues to evolve, businesses are increasingly recognizing the importance of incorporating ICT solutions to stay competitive in the digital age. IT Touch plays a vital role in helping businesses leverage technology to streamline operations, enhance productivity, and drive growth. Understanding the Role of IT Touch in growing your business IT Touch offers a range of technology solutions and support to businesses across various industries. Their expertise lies in understanding the unique requirements of each business and providing tailored solutions to address their IT needs. These services can include: IT infrastructure setup and maintenance Network design and implementation Hardware and software procurement and installation Data backup and recovery Cybersecurity solutions Cloud computing and virtualization IT consulting and project management Managed IT services The Benefits of Engaging ICT Solutions provider-IT Touch Partnering with IT Touch brings numerous benefits to your business: 1. Expertise and Experience IT Touch has a team of skilled professionals with expertise in various areas of technology. We stay updated with the latest trends and advancements in the industry, ensuring that businesses receive the best solutions and support. 2. Cost Savings Outsourcing IT services to us, a specialized company, eliminates the need for your businesses to invest in expensive infrastructure and hire and train IT staff. This results in significant cost savings, allowing businesses to allocate resources to other critical areas. 3. Enhanced Efficiency and Productivity By leveraging technology solutions readily available and provided by IT Touch, businesses can streamline their operations, automate processes, and improve overall efficiency. This leads to increased productivity and allows employees to focus on core business activities. 4. Data Security and Protection With the increasing threat of cyberattacks and data breaches, businesses need robust security measures in place. IT Touch implements comprehensive cybersecurity solutions to protect sensitive data, ensure business continuity, and safeguard against potential threats. 5. Scalability and Flexibility As your business grows, its IT requirements change. IT Touch offers scalable solutions that can adapt to the evolving needs of a business. This flexibility allows your businesses to easily upgrade or modify their IT infrastructure as required. Choosing the Right IT/ICT Services Company When selecting an IT/ICT services company, businesses should consider the following factors: 1. Expertise and Services Offered Ensure that the company has expertise in the specific services required by your business. Look for a comprehensive range of services that can cater to your present and future IT needs. 2. Reputation and Track Record Research the company’s reputation and track record in the industry. Check client testimonials and case studies to gauge their level of customer satisfaction and success stories. 3. Customization and Support Choose a company that can provide customized solutions tailored to your business requirements. Additionally, ensure that they offer reliable support and maintenance services to address any issues that may arise. 4. Security Measures Given the importance of data security, inquire about the company’s approach to cybersecurity and data protection. They should have robust measures in place to safeguard your business’s sensitive information. 5. Pricing and Value for Money Consider the pricing structure and evaluate the value for money offered by the IT/ICT services company. Compare quotes from multiple providers to make an informed decision. By engaging the services of a reputable IT/ICT services company like IT Touch, your business can harness the power of technology to drive growth, improve efficiency, and stay ahead in today’s competitive landscape.